Counter-Strike?
On Monday the Wall Street Journal ran a story on hacking back titled, “Support Grows to Let Cybertheft Victims Hack Back.” The article describes a growing desire to permit the private sector to retaliate against attackers. Being proactive is one thing, but the notion of enterprises retaliating against attackers is ludicrous. I honestly cannot understand why this topic is still in the public discourse. I thought debating this was so 2012. Legality is an issue, but so is the ability of companies to successfully conduct these types of operations without blowback.
The article explains, “… companies that experience cybertheft ought to be able to retrieve their electronic files or prevent the exploitation of their stolen information." I hate to be the bearer of bad news, but for most organizations, once the data has left your environment the chances of you retrieving it are very slim. Your data has left the building and it isn’t going to “re-spawn.” If you couldn’t prevent exfiltration of this data in the first place, what would make you think that you could prevent the subsequent exploitation of it?
As I said back in January in my “Five Steps To Build An Effective Threat Intelligence Capability” report, “If you have a mature security program, you can consider counterintelligence operations, but leave the hacking back to governments and militaries.”
There are many suggested strategies for dealing with the threat landscape. Hacking back should not be one.
- Crowdstrike tells us: “You don't have a malware problem, you have an adversary problem!” Crowdstrike has gone to great efforts to distance from the concept of hacking back (despite “strike” being in the company name.) CTO Dmitri Alperovitch wrote a blog on this in February titled “Active Defense: Time For A New Security Strategy.”
- Conversely, FireEye tells us that we need to focus on the malware. I had the opportunity to hear FireEye founder Ashar Aziz speak at the recent CEIC CISO/CLO Summit in Orlando. Much of the focus was malware; he told us, “Every 3 minutes malware activity is taking place on your network.”
No question, both are problems, but are they our biggest problem? No, the reality is we need to understand the data we are trying to protect first. This is foundational to all aspects of our business. Dossiers full of attacker TTPs serve their purpose, just as the ability to detect previously unknown malware is a key feature. However, if we don’t understand our assets we won’t have the context necessary to truly protect our enterprises. Forrester's Data Security And Privacy Playbook is designed with this in mind.
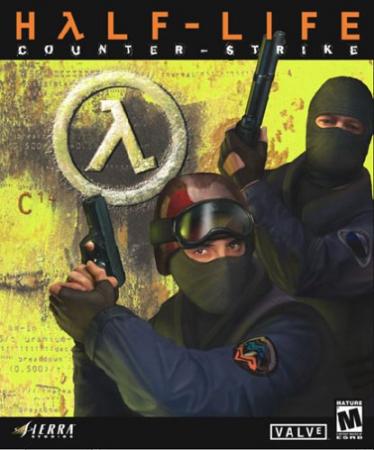
To wrap up, the only type of counter-striking enterprises should be engaging in should be done on a Valve server. (If you don’t get the Counter-Strike analogy, it is the one of the best first-person shooters ever created; check it out here.) Also, when it comes to data protection, “camping” is encouraged.