Enterprises In AP Must Build On Three Pillars To Manage BYOT Information Security
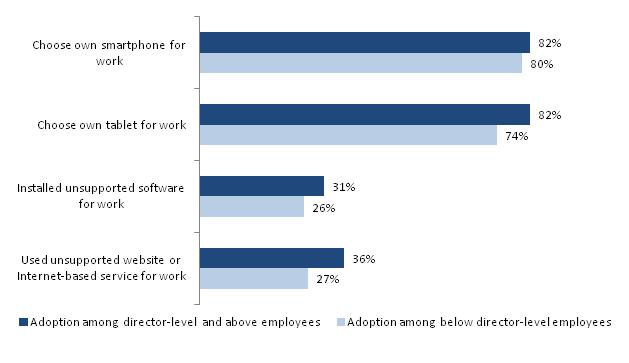
Information workers in organizations across Asia Pacific (AP) are increasingly using personal mobile devices, applications, and public cloud services for work. Forrester defines this as the bring-your-own-technology (BYOT) trend. This behavior is more prevalent among employees above the director-level (C-level executives, presidents, and vice presidents) than those below that level (individual worker, contractor or consultant and manager/supervisor). Data from Forrester’s Forrsight Workforce survey, Q4 2012 corroborates this trend in AP.
We believe that the BYOT trend will strengthen over the next two years in AP, primarily fueled by employees below the director level. Increasing options, quality and affordability of devices, apps, and wireless connectivity, coverage, and capacity will contribute to this expansion. In order to secure corporate data, organizations will need to:
- Develop Corporate Mobile Policies: Organizations must build cross-functional teams to plan their mobile strategies. This should include representatives from different LOBs like finance, HR, legal and sourcing. Moreover, the policy must clearly define guardrails to provide flexibility to employees but within boundaries and in compliance with local regulations.
- Identify Technologies To Secure Corporate Data: 29% of business-decision makers in AP report that the rising expectations of younger workers require businesses to push enterprise IT to keep technology current. This is why it is critical to identify both back-end and front-end technologies and suppliers that can optimize mobile device and application management in a secure manner. Focus should be on networking layer security and mobile device management solutions.
- Develop Improved Mobility Competencies: There is a dearth of mobile technology skills in AP and it will only worsen over the next two years. That is why organizations must start early and hire people with niche skill sets like Android and iOS app development to provision and manage mobility. In order to support the growing mobile devices connecting to the enterprise network, existing networking engineers and administrators must be trained in advanced WLAN skills. Finally, organizations should look at introducing new roles that focus on mobility such as chief privacy office and chief mobility officer.
My latest research report, Managing Information Security In BYOT Environments In Asia Pacific, covers these three key aspects in more detail and provides actionable advice to end-user companies on how to go about building on these foundations.
What do you think? I’d love to hear from organizations out there who have implemented or planning to implement their BYO program.