Navigating the Legal and Audit Implications of BYOD Initiatives
While the consumerization of IT marches on, in its footsteps lurks the specter of unknown risk. We live in a world of zero-sum games of litigation where suffocating regulations are the norm, and failure to comply can draw millions in fines and lawsuits. Technology diversity multiplies the challenge of maintaining compliance — it’s no wonder so many IT shops take a one-size-fits-all approach to workforce computing and forbid bring-your-own-device (BYOD). But it doesn't have to be this way. It’s possible to craft an approach that brilliantly achieves the conflicting goals of embracing BYOD and consumerization while slashing the risks and costs at the same time. Our recent research on the topic comes from working with lawyers and auditors who specialize in technology law and compliance reveals that it can indeed be done.
You Still Have to Act But the Cure is Often Worse Than the Disease
The technology attorneys we interviewed for this research agree — once you learn that BYOD is happening in your organization, you have a legal obligation to do something about it, whether you have established industry guidance to draw on or not. The answer is seemingly simple: Take action to stamp out the risk. However, the answer isn't that straightforward because:
- The more restrictions you put in place, the more incentive people will have to work around them and the more sophisticated and clandestine their efforts will be.
- There is no data leak prevention tool for the human brain, so arguably the most valuable and sensitive information walks around on two legs and leaves the building every night. Accepting this is important for keeping a healthy perspective about information risk on employee-owned devices.
Top BYOD Risks Include Intellectual Property Misuse, Accidental Data Loss
Intellectual property law violations can have especially severe repercussions. Patent, trademark, and copyright infringement are all very common but very difficult, if not impossible, to police with technical controls. For example, the willful and illegal misuse of someone else's property — misappropriation — sometimes comes into play when software is in use for business that isn't properly licensed and the attorneys can demonstrate that employees knew it and still continued to use it anyway. According to the law, not only can the firm be liable for past licensing fees, it can also owe damages equivalent to the value of every sale made after the first violation using the unlicensed software. Charles F. Luce Jr., partner at Moye White in Denver, says that the legal exposure of a firm is the same regardless of who owns the device.
Formal BYOD Guidance Is Immature And Open To Interpretation
Chris Gray, practice manager for Accuvant's risk and compliance business, says that regardless of who owns the device, when it's used in a regulated business, in theory it needs to adhere to the same regulations and industry standards as company-owned equipment. But he also notes that specific guidance for BYOD mobile device policies and technical controls are practically nonexistent. IT pros should also know that:
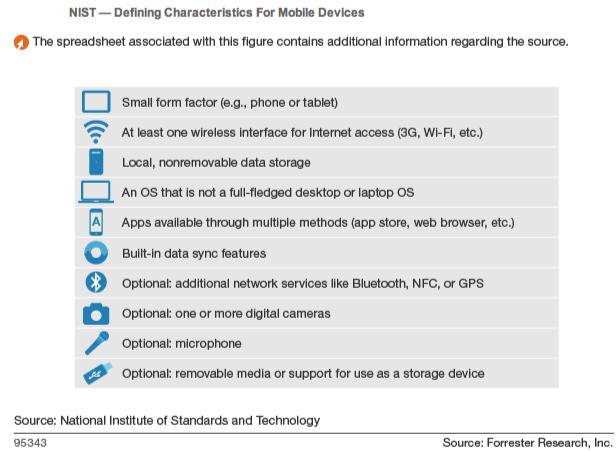
- Regulations are weak on technical controls, but ISACA, NIST, and PCI fill the gaps. Auditors look to US National Institute of Standards and Technology (NIST) technical control specifications for guidance, and it's often subjective because device and platforms evolve so quickly that it renders the guidance obsolete almost immediately.
- Tablets and smartphones live by a simpler set of rules. NIST Special Publication 800-124, published in July 2012 applies only to devices with "an operating system that is not a full-fledged desktop or laptop operating system," including smartphones and tablets. In essence it means that there is a different set of considerations for Windows 8 tablets for BYOD than for iPads — because Microsoft tablets such as the Surface Pro have a full-fledged laptop OS and iPads do not.
- Some standards, including PCI, specifically allow desktop virtualization. Payment Card Industry (PCI) standards are prescriptive for device configuration, management, security, access, and more, but PCI also has provisions specifically permitting the use of virtual terminals. Auditors generally interpret this to mean that terminal services (e.g., Citrix) and hosted virtual desktop infrastructures are acceptable because no payment card data actually resides on the device at any time.
Clear Policy And Education Form The Proper Foundation
Relying on technical controls alone is not effective, so effective BYOD governance starts with a clear policy and education. A signed BYOD agreement with each employee, along with adequate education on the risks and employees' responsibilities, are the absolute minimum. But electronically enforcing policies for employees incapable or unwilling to do their part is wise.
Take a Holistic Approach With Your BYOD Enablement Strategy
A viable BYOD strategy addresses culture, responsibilities, education, policy, and technical controls. It recognizes the value that BYOD brings to employee engagement and performance and features a clear agreement between the organization and each BYOD employee that outlines what each is responsible for. Technology's role is to help foster safe behaviors, control information access, and verify ongoing compliance — all without getting in the way of creativity, productivity, collaboration, or other daily activities.
Create a technology approach that promotes engagement while enforcing the policy. In most cases, this means keeping employee-owned devices off of the corporate trust network while allowing access to information through secure proxies and interfaces. In regulated environments, it also means sensitive data is never stored on employee-owned devices, but in less stringent environments, it can mean simply controlling access to systems of record such as customer databases to prevent anyone from walking away with a data dump. Firms doing this well know a lot about the nuances of a wide range of technologies and develop capabilities for offering a wide range of services and access.
For those of you responsible for BYOD programs where you work, what do you think? What are you learning as you work with legal and audit teams?
